-
Our Services
- AI with HKPC PICASSO
- The Cradle – Go Global Service Centre
-
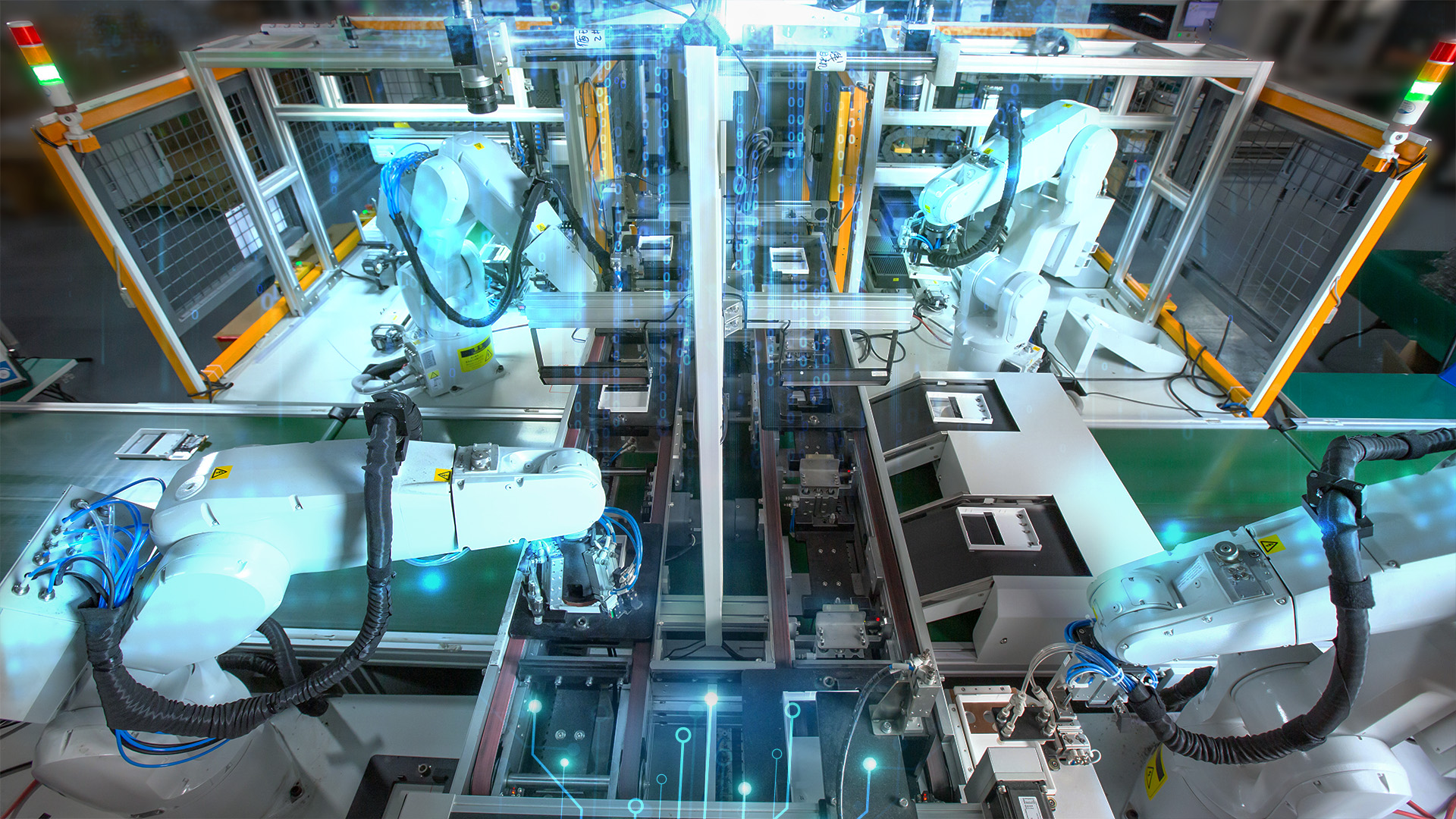
New Industrialisation
- New Industrialisation
- New Productive Forces Service Platform
- Smart Production Line
- Innovation Technology and R&D
- Transformation and Upgrading
- Nurture New Industrialisation Talent
- Rules and Regulations
-
HealthTech and Traditional Chinese Medicine
- HealthTech and Traditional Chinese Medicine
- R&D service and Functional Investigation on Chinese Medicine, Health Food & Wellness product
- Compliance Consultation Service for Chinese Medicine, Pharmaceutical, Health Food and Medical Device Industries
- Manufacturing Enhancement - Automatic Intelligent System for Production and Packaging in Chinese Medicine, Pharmaceutical and Health Food Industries
- Assisting funding application for local medicine and health industrial associations
- “The Cradle” Services for Health Tech and TCM Industry
-
Smart Manufacturing
- Smart Manufacturing
-
IIOT
- IIOT
- Industrie 4.0 - Smart Enterprise
- Product Lifecycle Management Consultancy
- Intelligent Automatic Warehousing and Logistics
- Real-Time Manufacturing Tracking System
- Knowledge Based Engineering & CAD Solution
- Location Based Services and Location Analytics
- The HATCH
- Hong Kong Industrial Drone Technology Centre
- Novel Materials
-
Advanced Manufacturing Technology
- Advanced Manufacturing Technology
- 3D Scanning and Reverse Engineering Service
- Flexible Metallic Fiber Physical Porous Part Fabrication Technology
- Advanced Mould Cooling Technology and CAE Conformal Cooling Analysis
- Gas Atomisation Technology
- Dual Laser Metal Polishing Technology
- Advanced Additive Manufacturing, 3D Printing Technology, and Direct Manufacturing
- Diffusion Bonding Technology
- Electrically-Assisted Free Forming (EAFF) Technology for Customisation of Sheet Metal Parts
- Plastic Process and Machinery Technology
- Fashion and Garment Technology
- Computer Aided Technology (CAx)
- Watch Assembly Automation Technology
-
Digital Transformation
- Digital Transformation
- HKPC Digital DIY Portal
- Digital Transformation Support
- Intelligent Integrated Non-wearable and Wearable Health Monitoring System and App for Elderly Homes
- 「FitEasy」Virtual Fitting Technology - For People with Disability
- Smart Solution
- Research and Analytics
- Strategic IT Management
- Embedded Software System
- New Media and Learning Technology Development
- IT Industry Support
- DevOps Maturity Assessment and Consultancy Service
- Software Testing Automation Consultancy Service
- Blockchain Consulting Service
- Extended Reality (XR) technology and consultancy service
-
Cyber Security
- Cyber Security
- Cyber Security
- Cybers Security-by-design, Privacy and Compliance-by-default
- Design & Architecture
- Train & Develop
- Offensive Security
- Intelligent Security
- Defensive Security
- Intelligent Hardening
- Internet of Things (IoT) & Operational Technology (OT) Cyber Security Testing
- Phishing Defence Services
- Cyber Security Assessment & Audit
- Cyber Security Consultancy for i4.0 & e4.0
-
Green & Smart Living
- Green & Smart Living
- Green Technology
- Food Technology
- Smart Living
-
Corporate Sustainability
- Corporate Sustainability
- ESG and Sustainability Services
- Manufacturing Technology (Tooling, Metals & Plastics) Recognition of Prior Learning (RPL) Mechanism
- Market Research and Analytics
- Business Innovation
- Sustainability-related standards and guidance
- Organisation Innovation Capability Development
- District Innovation
- Customer Service Assessment
- Intellectual Property (IP) Protection and Management
- Support to Creative Industries
- Manufacturing Standards Consultancy Service
- Production Capacity Optimisation
- Cost of Quality
- HKPC Academy
- SME Support
- Funding
- Testing & Standards
- Venues & Facilities
-
Support & Resource
- Technology Transfer
-
Support Centres
- Support Centres
- Circularity Research Centre
- Future Life and Health Tech Centre & Future FoodTech Lab
- Hong Kong Industrial Artificial Intelligence Robotics Centre (FLAIR)
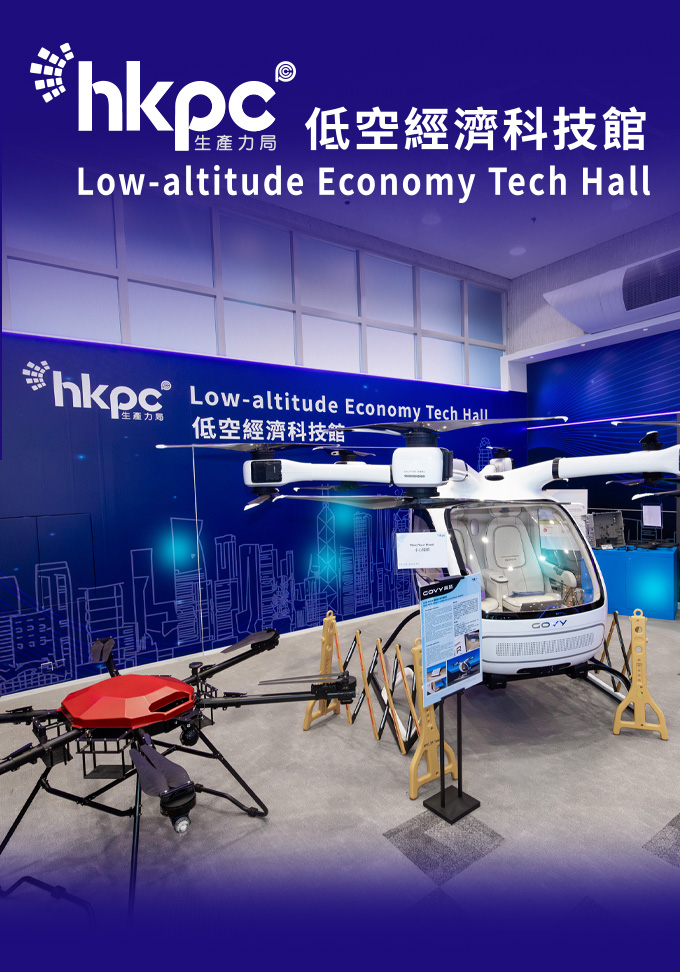
- Low-altitude Economy Tech Hall
- The Cradle – Go Global Service Centre
- Agentic AI and Industrial Metaverse Hall
- HKPC-HP 3D Printing Technology Centre
- Future Manufacturing Hall
- Hong Kong Technology and Innovation Support Centre
- Inno Space
- The HATCH
- Advanced Electronics Processing Technology Centre
- Green Living Laboratory
- Reliability Testing Centre
- Electromagnetic Compatibility Centre
- Plastics Technology Centre
- Smart Wearables, Watch & Clock Technology Centre
- Conformal Cooling Technology Centre
- Hong Kong Digital Testing Hub
- Hong Kong Industrial Drone Technology Centre
- Aqua Research Laboratory
- Advanced Materials and Intelligent Manufacturing Centre
- Hong Kong Joint Research Lab for Applications of Intelligent Automation Technology
- Future FoodTech Lab
- HKUST-HKPC Joint Research Lab for Industrial AI and Robotics
- Testing & Standards
- HKPC Spotlights
- About US
-
 LANGUAGE
LANGUAGE
HealthTech and Traditional Chinese Medicine
- R&D service and Functional Investigation on Chinese Medicine, Health Food & Wellness product
- Compliance Consultation Service for Chinese Medicine, Pharmaceutical, Health Food and Medical Device Industries
- Manufacturing Enhancement - Automatic Intelligent System for Production and Packaging in Chinese Medicine, Pharmaceutical and Health Food Industries
- Assisting funding application for local medicine and health industrial associations
- “The Cradle” Services for Health Tech and TCM Industry
IIOT
- Industrie 4.0 - Smart Enterprise
- Product Lifecycle Management Consultancy
- Intelligent Automatic Warehousing and Logistics
- Real-Time Manufacturing Tracking System
- Knowledge Based Engineering & CAD Solution
- Location Based Services and Location Analytics
- The HATCH
- Hong Kong Industrial Drone Technology Centre
Advanced Manufacturing Technology
- 3D Scanning and Reverse Engineering Service
- Flexible Metallic Fiber Physical Porous Part Fabrication Technology
- Advanced Mould Cooling Technology and CAE Conformal Cooling Analysis
- Gas Atomisation Technology
- Dual Laser Metal Polishing Technology
- Advanced Additive Manufacturing, 3D Printing Technology, and Direct Manufacturing
- Diffusion Bonding Technology
- Electrically-Assisted Free Forming (EAFF) Technology for Customisation of Sheet Metal Parts
- Plastic Process and Machinery Technology
- Fashion and Garment Technology
- Computer Aided Technology (CAx)
- Watch Assembly Automation Technology
Digital Transformation
- HKPC Digital DIY Portal
- Digital Transformation Support
- Intelligent Integrated Non-wearable and Wearable Health Monitoring System and App for Elderly Homes
- 「FitEasy」Virtual Fitting Technology - For People with Disability
- Smart Solution
- Research and Analytics
- Strategic IT Management
- Embedded Software System
- New Media and Learning Technology Development
- IT Industry Support
- DevOps Maturity Assessment and Consultancy Service
- Software Testing Automation Consultancy Service
- Blockchain Consulting Service
- Extended Reality (XR) technology and consultancy service
Cyber Security
- Cyber Security
- Cybers Security-by-design, Privacy and Compliance-by-default
- Design & Architecture
- Train & Develop
- Offensive Security
- Intelligent Security
- Defensive Security
- Intelligent Hardening
- Internet of Things (IoT) & Operational Technology (OT) Cyber Security Testing
- Phishing Defence Services
- Cyber Security Assessment & Audit
- Cyber Security Consultancy for i4.0 & e4.0
Corporate Sustainability
- ESG and Sustainability Services
- Manufacturing Technology (Tooling, Metals & Plastics) Recognition of Prior Learning (RPL) Mechanism
- Market Research and Analytics
- Business Innovation
- Sustainability-related standards and guidance
- Organisation Innovation Capability Development
- District Innovation
- Customer Service Assessment
- Intellectual Property (IP) Protection and Management
- Support to Creative Industries
- Manufacturing Standards Consultancy Service
- Production Capacity Optimisation
- Cost of Quality
Support Centres
- Circularity Research Centre
- Future Life and Health Tech Centre & Future FoodTech Lab
- Hong Kong Industrial Artificial Intelligence Robotics Centre (FLAIR)
- Low-altitude Economy Tech Hall
- The Cradle – Go Global Service Centre
- Agentic AI and Industrial Metaverse Hall
- HKPC-HP 3D Printing Technology Centre
- Future Manufacturing Hall
- Hong Kong Technology and Innovation Support Centre
- Inno Space
- The HATCH
- Advanced Electronics Processing Technology Centre
- Green Living Laboratory
- Reliability Testing Centre
- Electromagnetic Compatibility Centre
- Plastics Technology Centre
- Smart Wearables, Watch & Clock Technology Centre
- Conformal Cooling Technology Centre
- Hong Kong Digital Testing Hub
- Hong Kong Industrial Drone Technology Centre
- Aqua Research Laboratory
- Advanced Materials and Intelligent Manufacturing Centre
- Hong Kong Joint Research Lab for Applications of Intelligent Automation Technology
- Future FoodTech Lab
- HKUST-HKPC Joint Research Lab for Industrial AI and Robotics
Innovation — Green — New Productive Forces






HKPC Fully Supports SMEs
Six Key Support Services and Measures to Help SMEs Overcome Challenges
LEARN MORE


BIZ Expands Easy Launches Mobile App “BEE@HKPC”
Government Funding Scheme at Your Fingertips
DOWNLOAD NOWServices
News & Events
SUBSCRIBE TO OUR NEWSLETTERS
Share the latest information of HKPC to your inbox
Our Services
Support & Resource
HKPC Spotlights
Privacy
Terms of Use
Occupational Health & Safety Policy
(PDF version)
Service Arrangement under Adverse Weather
Sitemap
Contact Us
COPYRIGHT© Hong Kong Productivity Council